In this first section of Cryptography & Network Security you will get to read about What is Cryptography, its process, What is Encryption, What is Decryption, Advantage, and Disadvantage and Application of Cryptography. So let’s start.
What is Cryptography
Cryptography is a subject that is used to protect the user’s data and increase the security of the network. Cryptography is mostly read and learn by students of information technology (I.T) or Computer Science & Engineering (CSE).
The word Cryptography is derived from the Greek word Krypto, which means Hidden or Secrets. That is, cryptography is the secret way to keep your data, cryptography means The Art of Protecting Data. That is how we have to keep our data secret so that no one else can read it. Our data can be of different types like a credit card, debit card information, any website login credential, etc.
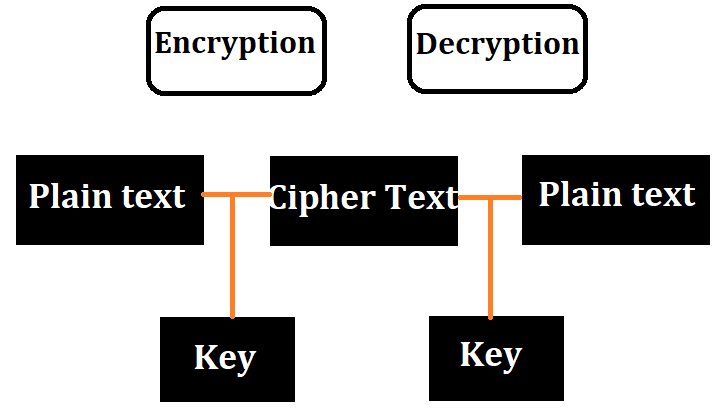
Through cryptography, we can convert our data into Unreadable Secret Codes, which no one can read, that Unreadable Secret Codes we call Cipher Text. But the person who has the secret key can read that data, the person can decrypt the data by that secret key, the decrypted data is called plain text. In this, there are two processes of Encryption and Decryption, which are used to protect the data. In Encryption, the data is converted from plain text to Cipher Text so that no one can read and in Decryption encryption causes the reverse process. In this, the data is converted from Cipher Text to Plain Text so that everyone can read.
The Process of Cryptography
There are two process –
- Encryption
- Decryption
What is Encryption
Encryption is a process of cryptography. It is used to keep user’s data secret. This is a method that is used to convert data and information into secret codes this is called cipher text. Cipher text is a text that no one can understand and the original data that we have is called plain text that everyone can read and understand.
- The main purpose of encryption is to keep the data secure.
- To read encrypted data you must have a public key.
Encryption basically consists of two types the first one is Asymmetric encryption and the second one is Symmetric encryption.
What is Decryption
Decryption is a process of cryptography. It is used to decrypt, encrypted data. Decrypted data or original data is called plain text. That is, converting Cipher text to plain text is called Decryption. To convert Cipher text to plain text we need a key so that we can convert the data into readable form.
Advantage of Cryptography
- Confidentiality – Cryptography techniques can keep any type of information confidentiality and protect it from unauthorized users.
- Authentication – This is a technique of cryptographic with the help of which we can protect the information of MAC and digital signatures.
- Data Integrity – The hash functions of cryptographic help in assuring the user’s data.
- Non-repudiation – Cryptography does not accept non-repudiation requests at the time of a digital signature.
Disadvantage of Cryptography
- A non-functional attack may be carried out by an intruder on a network or computer system.
- Through the use of cryptography, it cannot be ensured that the data used by the users are really secure.
- Cryptography does not provide security from threats arising from bad systems, protocols, and processes.
- Cryptography is a costly technology that is in terms of time and money.
Application of Cryptography
- Authentication/Digital Signatures – From Authentication and Digital Signatures though we can find out whether the data sent by the sender is authenticated or not.
- Time-stamping – This is a technique through which we can find out at what time an electronic document was distributed.
- Electronic Money – Electronic Money is a technique of cryptography that identifies money transactions by net transfer.
- Encryption/Decryption in email – Encryption, and Decryption are mostly used at the time of mailing so that the data of the users can remain secure.
- Encryption Social Media – In today’s time, every social media uses encryption techniques so that the user’s data can be kept secure.